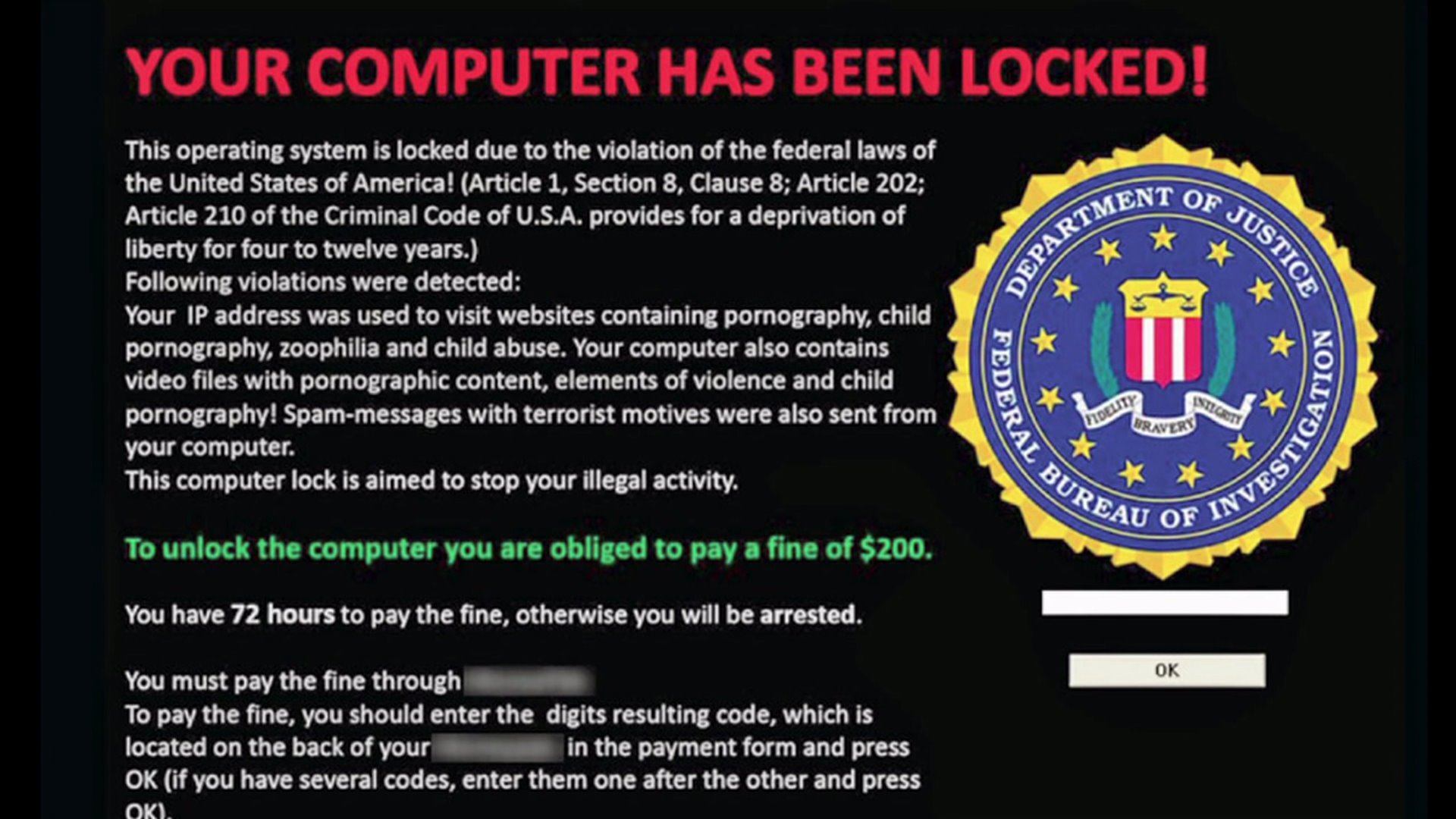
Ransomware is a digital attack in which an executable or malicious link opened by an unsuspecting user installs a program that blocks access to applications, phone systems, and/or data until a ransom is paid.
Ransomware is nothing new, in fact it’s been around for years but as of late, hackers have begun zeroing in on a specific vertical: state and local governments.
In recent years, over 200 state, county and city governments have been targeted by ransomware attacks.
With thousands of cities across the US, that may not sound like a lot, but it is becoming increasingly more prevalent and those numbers are growing every single day as attackers specifically target government agencies.

22 governments have been effected by ransomware in 2019 alone and this news came after 22 small town in Texas were targeted in a single, coordinated attack.
Ransomware is becoming easier and easier to distribute and attackers are doing a really good job at deceiving unsuspecting users into unknowingly opening files and documents that are malicious.
Ransomware is distributed to users via e-mail attachments, phishing e-mails, or web-exploits without the user even knowing what is happening in the background until the malicious malware is already delivered.
For example, your accounting team may receive and attachment via e-mail that looks legitimate.
When they download the “invoice” the malicious malware penetrates and infects the system.
Ransomware attacks can be that simple. The user doesn’t even need to actually visit a web site to become infected, it can be sent to them through a very realistic e-mail.
Why are Governments Becoming a Target for Ransomware?
Government have become a popular target for ransomware for a few different reasons and the main one being that they have more lax information security standards and training than many for-profit organizations.
This is usually due to a lack of funding in the IT areas.
The lack of training and education on ransomware, phishing, and other cyber attacks makes them an easy target because employees simply are not educated enough to recognize the sophisticated attacks.
Furthermore, government agencies work closely with other departmental systems and branches which makes them an ideal target so malware can easily spread and have a bigger impact.
They also maintain crucial safety systems and public services that simply cannot afford downtime.
Many government agencies will just pay the ransom without trying to fight it because they simply cannot afford the down time, they need the systems back up and running as soon as possible.
Some of the attacks this year include cities like Baltimore, Lake City, Florida, and a few towns in Texas.
Hackers have demanded ransoms of $76,000 USD (13 bitcoins) all the way up to $2.45 million USD for the larger government agencies in one of the towns in Texas.
Although the US Conference of Mayors agreed to refuse payment of ransomeware attacks, paying the ransom is a quick and easy way to get your files and system back up and running.
If the ransom demand is fairly low, government agencies are more likely to just pay it.
An emergency IT resolution system, training and updated security implementations could cost tens of thousands of dollars.
As an example, Atlanta was recently hit with a $52,000 ransomware attack and they refused to pay the ransom.
The cleanup ended up costing over $2.6 million dollars.
Although paying the $52,000 seemed like it would have been a better option in hind sight, paying up can encourage future attacks.
There is also no guarantee that the hackers won’t just take the money and not return the files and access to your systems.
Once ransomware has been installed, there are usually two options:
- Pay the ransom
- Refuse the ransom and try to get your files and systems back on your own
If you don’t maintain proper backups and don’t have a disaster recovery environment setup, refusing the ransom could mean you may need to start your entire IT infrastructure from scratch.
For government agencies, this means major downtime of critical pubic resources for safety and services.
If you do have a proper backup and recovery environment, refusing the ransom still requires a lot of work to retrieve the files and systems and secure the network. This could cost a-lot of money, as we saw in the Atlanta ransomware case.
This is why local and state governments are starting to ramp up their IT Monitoring to thwart ransomware attacks.
The first major step that government agencies are taking to help prevent these malicious attacks are by education their staff.
By education their staff on what to look for, they are providing phishing and social engineering training.
The most common way that ransomware is installed is through e-mail attachments and through clicking and opening e-mail links.
The next major step is to make sure IT systems have leading antivirus and anti-malware tools installed on every workstation and server.
Lastly, and of equal importance, is having a rock solid backup and disaster recovery plan in place so that if a ransomware does slip through the cracks, you are covered and are able to get your files back.
This allows you to bring the systems back up where you left off, or at least close to where you left off before the attack.
Some government agencies are even purchasing cyber-insurance to help protect them if there is a ransomware attack.
Cyber-insurance help organization recoup some of the costs associated with a ransomware attack or other type of cyber attack.